When you unlock your iPhone or pass through an airport’s biometric gate, you rely on a complex system. That system is facial recognition.
Today, facial recognition has become a common part of modern security and convenience. But how does facial recognition work behind the scenes? Or, why do so many companies trust it for security and access control?
This blog explains the reason behind it and provides a detailed guide on the essential steps of facial recognition. We will explore its real advantages and how it compares with other authentication methods like passwords, PINs, and OTPs.
What is facial recognition?
Facial recognition is a biometric technology that uses an individual’s unique facial features to identify or verify their identity. In simplest words, it answers one primary question: ‘Who is this person?’ (identification).
Unlike simple image matching, it involves analyzing the specific geometry, contours, and spatial relationships of facial landmarks to create a mathematical representation, often called a faceprint or facial template. This blueprint is then used for comparison against stored data.
One can call it a form of advanced intelligence, specifically a subset of computer vision, that automates the human ability to recognize faces but at a scale, speed, and consistency impossible for humans to achieve manually.
Facial recognition vs facial authentication
While often used interchangeably, these terms have distinct meanings.
Facial recognition asks, ‘Who is this person?’ It searches through a database of many faces to find a potential match. Facial authentication asks, ‘Is this the claimed person?’ It performs a one-to-one check, comparing a face against a single, pre-registered template. In essence, recognition is about identification within a group, while authentication is about verifying a specific claim of identity.
| 👀Did you know? Advanced face recognition technology now acts as a 24/7 co-pilot in vehicles. By analyzing eye position, blink rate, and head tilt, these systems detect driver fatigue (a cause of one in six serious accidents) and issue immediate warnings to prevent collisions. |
How does facial recognition work?
Facial recognition systems follow a specific sequence to verify an identity. Here is a glance of the core steps:
- Image acquisition and face detection
The system begins by obtaining an image or video frame from a camera. The first algorithmic task is face detection, which isolates the human face from the background clutter. Using techniques like Haar cascades or deep learning-based detectors (e.g., Multi-task Cascaded Convolutional Networks), the system locates the face, often drawing a bounding box around it.
This step simply answers, ‘Is there a face in this image?’
- Face pre-processing and alignment
A raw detected face can be tilted, poorly lit, or partially obscured. Pre-processing standardizes the image to improve downstream accuracy.
This includes:
- Alignment: Rotating and scaling the face so key features (like the eyes and mouth) are in a consistent position.
- Normalization: Adjusting for lighting and contrast variations to ensure the analysis focuses on structural features, not environmental artifacts.
- Cropping: Focusing the region of interest on the core facial area.
- Feature extraction and template creation
Here, the system analyzes the pre-processed face to map its unique characteristics. Deep learning networks analyze the pre-processed image, measuring key distances and shapes like the distance between the pupils, the depth of the eye sockets, the shape of the cheekbones, and the contour of the jawline.
This complex set of measurements is condensed into a unique numerical vector or template. This template is not a stored image; it’s an irreversible mathematical representation. It cannot be reverse-engineered to recreate a photo, which is a key privacy safeguard.
- Comparison and matching
The generated template is now ready for its purpose. For authentication (1:1), it is compared against a single stored template associated with the user’s claimed identity (e.g., the template created when you first set up Face ID).
For identification (1:N), it is searched against an entire database of templates. The system calculates a similarity score (e.g., cosine similarity, Euclidean distance) between the presented template and the stored template(s).
- Decision and action
The final step is a business-logic decision based on the similarity score. A pre-defined threshold determines the outcome. If the score is above the threshold, it’s a match; if below, it’s a non-match.
This threshold is tunable based on the use case’s security requirements. A high-security facility might set a very high threshold, accepting a slightly higher false rejection rate for near-zero false acceptances. A consumer photo tagging app might use a lower threshold for convenience. Let’s now move to learn about different face recognition systems.
Types of facial recognition systems
Not every facial recognition system is built for the same task or environment. Below, we break down different face recognition systems:
2D vs 3D facial recognition
2D facial recognition studies visible features like the distance between eyes, jawline, and contrast patterns in pixels. This method depends heavily on lighting, camera angle, and facial expressions, which can affect results.
3D facial recognition, on the other hand, reads depth. It maps the actual shape of the face using sensors that capture contours like nose height and chin structure. Because it understands depth, it performs better in low light and resists photo-based attacks. This approach is common in high-security devices, including modern smartphones.
Active vs passive recognition systems
Active systems need a person’s direct participation. The individual must consciously look at a designated camera and pause, as when unlocking a phone or passing through an automated airport gate. This cooperation provides a clear, consistent image optimized for accurate verification.
In contrast, passive systems operate without a person’s knowledge or consent. Cameras in public areas, stores, or transportation hubs scan faces as people move naturally. This method is typically used for surveillance or identifying individuals in a crowd, leading to considerable debate about public privacy.
Verification (1:1) vs identification (1:N)
- Verification (1:1): ‘Am I who I say I am?’ Compares one probe template to one reference template. The result is a binary yes/no. It’s faster, more private (no large database search), and is the standard for authentication use cases.
- Identification (1:N): ‘Who is this person?’ Compares one probe template against N templates in a database. The result is a candidate list of potential matches ranked by similarity score. Complexity and processing time scale with database size (N).
How secure are facial recognition systems?
A system’s security depends on its design and deployment. Leading consumer systems, like the face unlock on your phone, keep your unique facial template locked in a special chip on the device itself. The data never leaves your possession, and verification happens locally.
This ‘on-device’ approach minimizes the risk of large-scale database breaches. For broader systems used in security or enterprise settings, security is managed through strong encryption, strict data access controls, and built-in privacy safeguards.
Where is your data stored?
This is the most important question. If the biometric template is stored and processed directly on your device, the risk of external theft is very low. In server-based systems, your template is encrypted both during transmission and while stored, protected by the same standards that secure other sensitive data.
Can it be tricked?
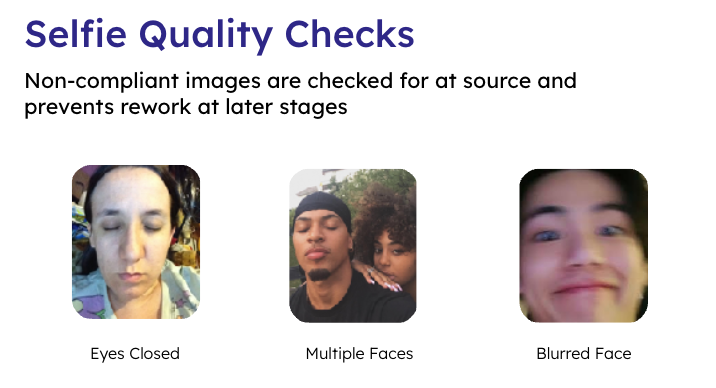
Yes, without proper countermeasures. A simple photo or video can fool a basic system. This is why ‘liveness detection’ is essential. Modern systems check for subtle signs of life, like micro-movements and skin texture, to ensure they are scanning a real person, not a static image or a mask.
How accurate and fair is the technology?
While modern algorithms can be extremely accurate under good conditions, their performance hasn’t been equal for everyone. Historically, systems trained on limited datasets have had much higher error rates for women, people of color, and older individuals. This isn’t a flaw in the core technology, but a failure in how the training data was gathered.
Responsible development now focuses on using globally diverse data to achieve fairness and high accuracy for all users
Benefits of facial recognition for businesses and industries
Moving beyond its complex mechanics, the real value of this technology lies in its tangible impact on businesses and industries.
- Benefits of facial recognition for businesses
For commercial enterprises, the value proposition is clear and measurable:
- Security and fraud prevention: Replaces easily lost, stolen, or shared credentials. Unique biometrics significantly reduce account takeover fraud and ‘tailgating’ in physical spaces.
- Faster user experience: Eliminates password recall and reset headaches. Authentication can occur in 0.2 seconds, directly improving customer conversion and activation rates during onboarding.
- Scalability and cost efficiency: Automates manual verification, reducing labor costs and operational overhead.
- Benefits of facial recognition in law enforcement
With proper legal oversight, it can accelerate suspect identification, help locate missing persons and victims of human trafficking, and aid in exonerating the innocent by providing digital alibis through video evidence.
- Benefits of facial recognition in healthcare
It secures health information by ensuring only authorized personnel have access to patient records. It accurately identifies patients to prevent dangerous medication errors and streamlines patient registration.
It can also be used for remote patient monitoring and adherence checks.
- Benefits of facial recognition for security
In sectors like critical infrastructure, data centers, and manufacturing, it provides non-transferable, audit-ready access control. It enables ‘hands-free’ authentication in sterile environments (e.g., labs, clean rooms) and can be integrated with time-and-attendance systems to eliminate ‘buddy punching.’
| 🙂 Fun Fact: In some parts of China, facial recognition is used for far more than security; it can authorize subway fares, allow students to clock school attendance, and even dispense toilet paper in public restrooms to prevent overuse, showcasing its integration into daily life! |
Challenges and limitations of facial recognition
Despite its power, this facial recognition technology isn’t a flawless solution. Below are some commonly discussed limitations:
- Privacy and ethical governance
The primary challenge is not technical but societal. The potential for mass surveillance and use without informed consent can create significant ethical and legal risks.
Organizations must develop clear, transparent policies on data usage, retention, and sharing, aligning with regulations like GDPR, BIPA (Illinois), and emerging AI acts.
- Regulatory and legal compliance landscape
The regulatory environment is fragmented and must navigate a complex web of local, national, and sector-specific laws governing biometric data collection. A solution that is compliant in one jurisdiction may be illegal in another.
- Technical limitations and environmental factors
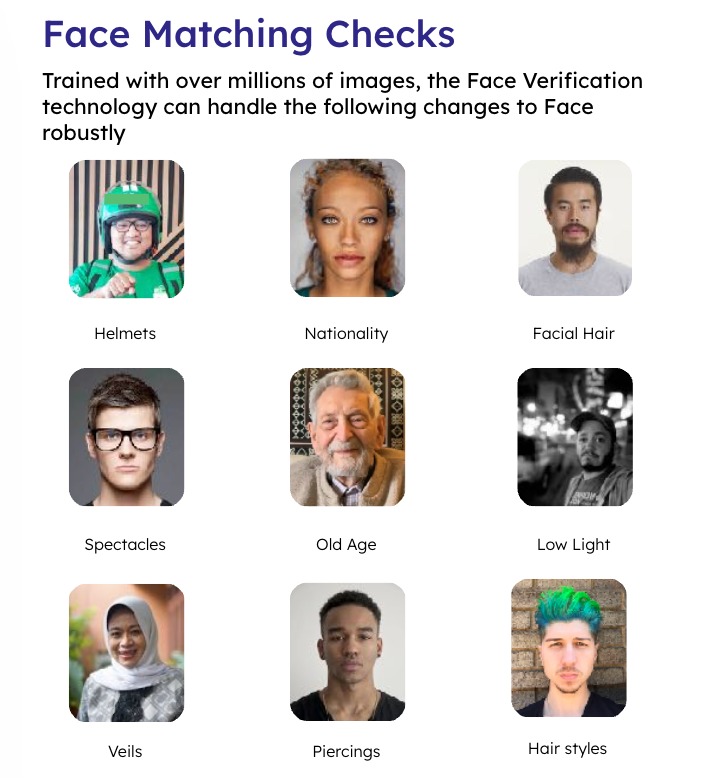
Performance can degrade with significant changes in appearance (aging, surgery, heavy makeup, facial hair), extreme angles, poor lighting, or low-resolution cameras. While technology is improving, these factors must be considered in system design and threshold setting.
- Vulnerability to sophisticated deepfakes and adversarial attacks
As the technology advances, so do attack vectors. Highly realistic deepfakes and adversarial techniques that subtly alter facial images to fool AI models represent an ongoing arms race, requiring continuous investment in defensive R&D and liveness detection.
How is HyperVerge leading the race in advanced facial recognition technology?
For enterprises demanding a proven solution, HyperVerge delivers industry-leading facial recognition technology trusted by global clients like Vodafone, SBI, and Grab.
HyperVerge’s approach addresses key enterprise requirements:
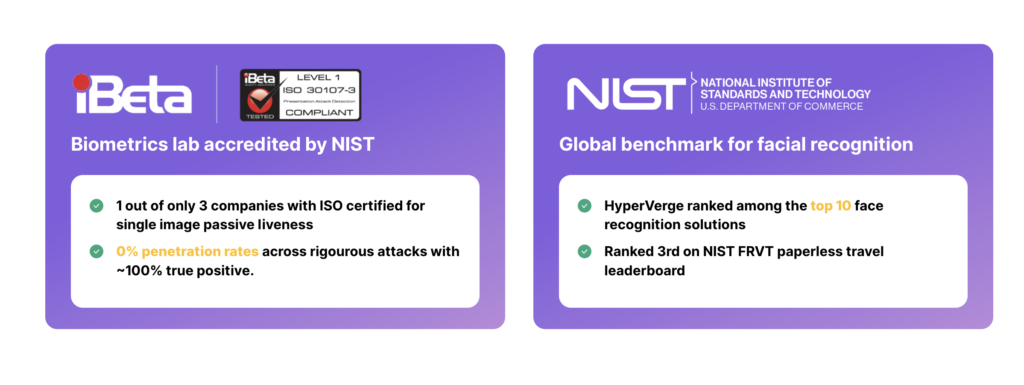
- Certified excellence: Ranked in the top 10 globally for Facial Recognition algorithms by NIST and holding iBeta certification for passive liveness detection, ensuring both accuracy and security are independently validated.
- Superior user experience: Its passive liveness requires no gestures, enabling authentication in 0.2 seconds and driving a 95% straight-through processing rate. This focus on convenience has helped clients reduce drop-off rates by 50%.
- Equitable technology: AI models are specifically trained on a diverse database to be devoid of bias across races, ages, and genders, ensuring fair and accurate outcomes for every user.
For leaders evaluating a state-of-the-art identity and facial recognition system, HyperVerge represents a benchmark. Sign up with HyperVerge today, explore how advanced facial authentication can transform your business’s security