The importance of safeguarding sensitive information online cannot be overstated in today’s world. A single password cannot be the only protection against intruders for your personal and financial data. Sounds risky, right? Enter multi-factor authentication (MFA).
This additional layer of security in user authentication fortifies accounts beyond the conventional password. But what exactly is multi-factor authentication, and how does it work to secure your digital life? Let’s delve deeper into this modern-day digital knight, its operations, and how it shields your accounts from potential breaches.
What is Multi-factor Authentication?
Authentication factors are methods used to verify a user’s identity before granting access to information. Traditional authentication relies on something you know, like a password. However, hackers can easily compromise this using various techniques such as phishing or brute force attacks. This can lead to unauthorized access to your accounts and sensitive information.
Multifactor authentication adds an extra layer of security by requiring a second form of verification, something you have. This could be a physical item like a smartphone or a token generator, making it much harder for hackers to gain access even if they know your password.
Advanced multifactor authentication methods, such as adaptive authentication, enhance security by using risk-based authentication for access control. Instead of using a one-size-fits-all authentication method, adaptive authentication takes into account contextual information and user behavior to determine the appropriate level of security needed.
Read more about user authentication here.
Three Types of MFA Authentication Factors
Multifactor authentication (MFA) uses multiple authentication factors to prove a user’s identity before granting them system access.
These authentication factors usually fall into three categories: something you know, something you have, and something you are.
Something You Know (Knowledge Factor)
“Something you know” refers to the traditional form of password-based authentication, where you provide a secret phrase, PIN, or an answer to a security question. This information should be unique and known only to you.
However, as mentioned earlier, this method on its own can be vulnerable to hacking attempts, hence the need for an additional layer of security provided by multifactor authentication.
Something You Have (Possession Factor)
“Something you have” is the second authentication factor in MFA, typically referring to a physical device in your possession or “possession factor authentication”. A typical example is receiving a temporary SMS code or using a dedicated multi factor authentication technology app that generates timed codes.
These codes are unique to a user’s mobile device, and expire quickly, dramatically reducing the chances of unauthorized access. This method leverages the reduced likelihood of a hacker accessing both your password (something you know) and your specific physical device (something you have).
Related read: A complete guide to phone verification
Something You Are (Biometric Factor)
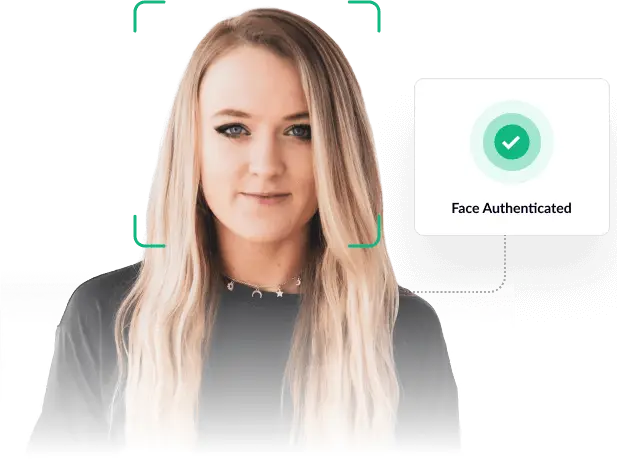
“Something you are” is the third and final layer of multi-factor authentication. This factor requires biometric identity verification, rather than a physical device, for example, fingerprint scanning or facial recognition. As humans, we’re unique, so our facial features and fingerprints are difficult to replicate.
How Does Multi-factor Authentication Work: MFA Authentication Methods
Now that we’ve established the necessity for multifactor authentication let’s delve into the different types. Understanding these types will help you decide the most suitable protection for your specific needs.
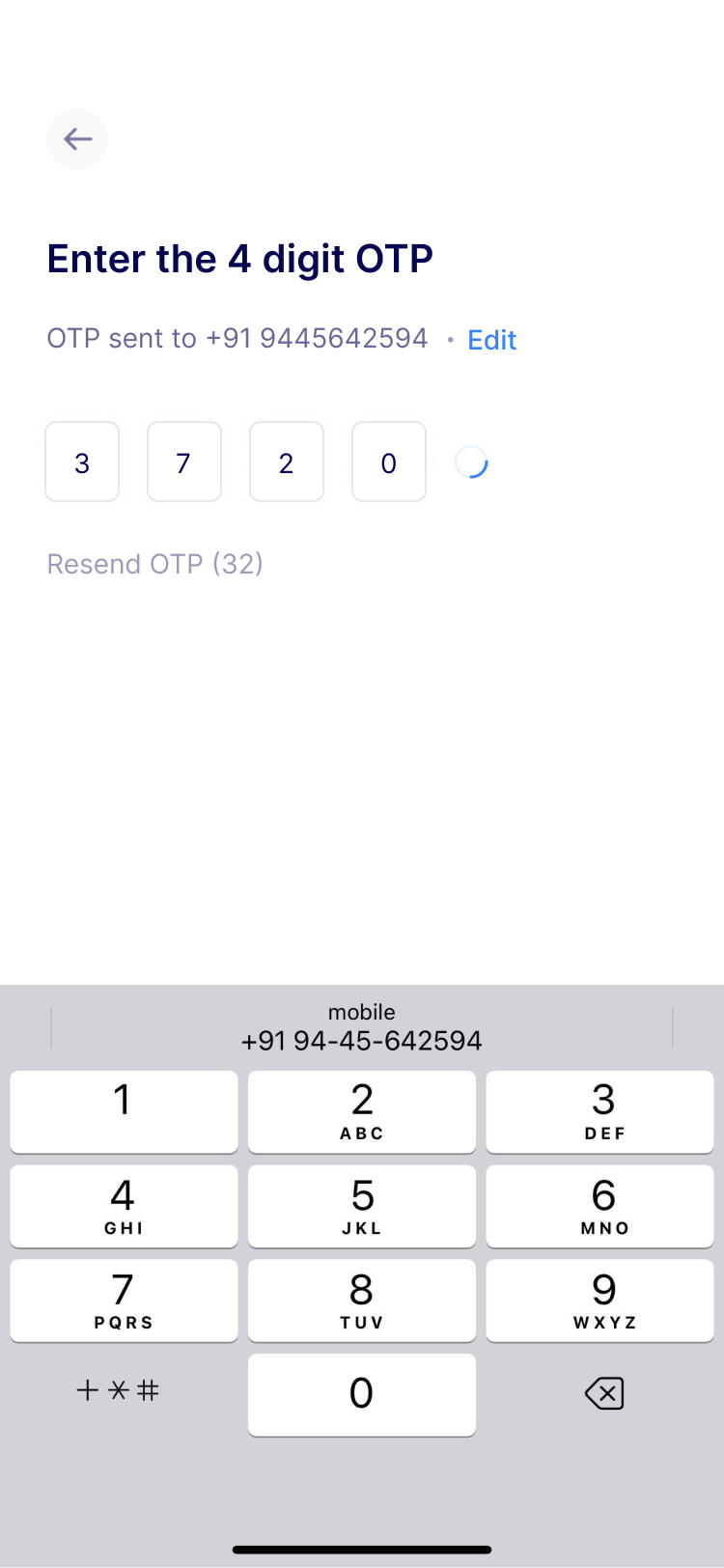
- SMS-Based Authentication: A text message sends an authentication code to the user’s registered mobile number. This code needs to be entered to complete the authentication process.
- Email Verification: A unique code or a link is sent to the user’s email address. Access is granted after the user clicks the link or enters the code on the platform.
- Biometric Authentication: This method uses unique biological characteristics, like fingerprints, facial recognition, or iris scans. These attributes are unique to each individual, providing a strong layer of security.
- Hardware Tokens: These are physical devices that generate time-sensitive codes. The user needs to enter this code to gain access.
- Software Tokens: Similar to hardware tokens, these applications generate unique codes. The difference is that these are digital and can be installed on a user’s device.
Read more about facial recognition in our detailed guide here.
Why is Multi-Factor Authentication Important?
In a hyper-connected world, the frequency and severity of cyber threats and data breaches escalate alarmingly. Armed with sophisticated tools, malevolent actors constantly look for weak spots in digital systems.
Personal data, corporate secrets, financial information – nothing is off-limits. High-profile breaches frequently make headlines, serving as a stark reminder of the pervasive risks lurking in the digital landscape.
Relying solely on passwords for account protection presents significant limitations. No matter how complex, passwords are susceptible to breaches via brute force attacks, phishing scams, and even simple human errors such as sharing or writing them down.
Furthermore, many users resort to easily guessable passwords or reuse them across platforms, creating a domino effect in case of a single breach. This leads to inadequate security, making two-factor authentication not just an option but a necessity.
Benefits of Multi-Factor Authentication?
Multi-factor authentication presents numerous advantages that significantly enhance your account’s security:
- Enhanced Security: By requiring a second form of verification, multi-factor authentication makes it significantly more challenging for unauthorized users to access your account.
- Data Protection: With the added layer of security, sensitive data within your account is better protected against breaches.
- Minimise Fraud: Multi-factor authentication also helps reduce identity theft and fraud as it complicates the impersonation process.
- Cost-Efficient: While providing strong security, multi-factor authentication methods like SMS and email verifications can be implemented cheaply.
- User Awareness: In case of unauthorized access attempts, users get instant alerts, fostering vigilance and immediate response.
- Accessibility: Most two-factor authentication methods are user-friendly, requiring a few extra seconds to secure your account.
Thus, we can see that two-factor authentication not only offers improved security measures but also provides added benefits to both businesses and individuals. It is an essential tool in maintaining the integrity of accounts and protecting sensitive information.
What are the Common Misconceptions About Multi-Factor Authentication?
Common misconceptions about two-factor authentication often revolve around its perceived inconvenience. While it’s true that this layer of security requires an extra step, the inconvenience is minor compared to the robust protection it provides.
In most cases, the additional security step is as simple as inputting a code received on your mobile phones or clicking a verification link in your email. Therefore, the trade-off between a minimal increase in effort and a significant enhancement in security makes two-factor authentication a necessary measure in this digital age.
How to Implement a Multi-factor Authentication System
Implementing a multi-factor authentication (MFA) system is a crucial step in enhancing the security of your applications and systems. MFA adds an extra layer of protection by requiring users to provide multiple factors of identification before gaining access. Here’s a general guide on how to implement a multi-factor authentication system:
1. Choose MFA Methods
a. Something You Know (Knowledge Factor):
– Passwords or PINs.
b. Something You Have (Possession Factor):
– One-time passwords (OTP) sent via SMS, email, or generated by authenticator apps.
– Smart cards or physical security tokens.
c. Something You Are (Biometric Factor):
– Fingerprint scans.
– Retina scans.
– Face recognition.
2. Select MFA Providers:
Choose a reliable MFA provider or library that supports the methods you’ve selected. Some popular providers include:
– Google Authenticator
– Authy
– Duo Security
– YubiKey
3. Integrate MFA into Your Application:
a. Backend Integration:
– Modify your authentication system to support MFA.
– Implement APIs or SDKs provided by your chosen MFA provider.
b. Frontend Integration:
– Update your login interface to prompt users for additional authentication factors.
– Implement user interfaces for managing and configuring MFA settings.
4. Store and Manage MFA Secrets Securely:
If you’re using one-time passwords or similar methods, securely store and manage the secrets associated to create passwords with each user. This is crucial to prevent unauthorized access.
5. Enable MFA Recovery:
Implement a secure method for authorized users to recover access in case they lose their second factor. This could involve backup codes or alternative recovery methods.
6. Test and Monitor:
Thoroughly test your MFA implementation to ensure it works as expected. Monitor logs and user activities to detect any unusual patterns or potential security breaches.
7. User Education and Communication:
Educate users about the importance of MFA and guide them through the setup process. Clearly communicate any changes to the login process and provide support for any issues they may encounter.
8. Compliance Considerations:
Ensure that your MFA implementation complies with relevant regulations and standards, especially if you’re dealing with sensitive data or in regulated industries.
9. Regularly Update and Improve:
Stay informed about the latest security standards and threats. Regularly update your MFA system to incorporate new features and address potential vulnerabilities.
10. Legal and Privacy Considerations:
Understand and comply with legal and privacy requirements related to user authentication. Ensure that you handle user identities and data securely and transparently.
Implementing a multi-factor authentication system is a crucial step in securing your applications. The specific steps may vary based on your technology stack and the chosen MFA methods, so always refer to the documentation provided by your selected MFA provider.
Conclusion
Multi-factor authentication is a crucial security measure in today’s digital landscape. Despite minor inconveniences, it offers robust protection for online accounts, shielding sensitive information from potential cyber threats. Regularly updating these settings and safely storing backup codes further fortifies digital security.
Remember: Don’t wait until it’s too late! Embrace multifactor authentication today for your online accounts. It’s a straightforward yet powerful way to shield your sensitive data from prying eyes and thwart cyber threats. Be proactive in enhancing your digital security – your future self will thank you!
To know how you can implement biometric verification using facial recognition, head here!