User authentication serves as the gatekeeper of our digital identities, determining who is allowed access to sensitive data and systems. It is a fundamental aspect of cybersecurity, a bulwark against unauthorized access that ensures that only verified individuals can enter the digital spaces that are increasingly integral to our daily routines.
According to Verizon’s 2023 Data Breach Investigations Report, external threat actors were responsible for 83% of breaches, with 74% of all breaches including a human element, such as stolen login credentials or social engineering attacks. Thus, credentials are a significant vulnerability, with 61% of breaches involving user credentials. By understanding the nuances of user authentication, we can better appreciate its role in safeguarding our digital lives and the collective cyberspace we all share.
What is User Authentication?
User authentication is a cornerstone of information security, ensuring that access to hardware, software, and data is safeguarded against unauthorized users. Authentication process verifies the identity of a user or entity attempting to gain access to a system, network, or device. This verification process is critical in establishing trust in the digital world, where the user is not physically present to identify users confirm their identity.
Authentication vs Authorization
Authentication and authorization are often used interchangeably, but they serve different purposes in security architecture.
Authentication verifies who a user is.
Authorization determines what that authenticated user is allowed to do.
For example, when a customer logs into a banking app, authentication confirms their identity using credentials or biometrics. Authorization then decides whether they can view account balances, transfer funds, or access investment products.
In modern digital systems, authentication always precedes authorization. Strong identity verification ensures that access control policies are applied to the correct user.
How Does User Authentication Work?
User authentication works by verifying a user’s identity to ensure they are who they claim to be before granting access to a system or service. This process based authentication can be broken down into several steps:
- Identification: The user claims an identity, typically by entering a username.
- Verification: The system validates the identity claim by checking one or more factors.
- Something the user knows (e.g., a password or PIN),
- Something the user has (e.g., a security token, a smartphone with an authentication app, or a hardware key),
- Something the user is (e.g., biometric characteristics like fingerprints or facial recognition),
- Somewhere the user is (e.g., geolocation or IP address verification),
- Something the user does (e.g., typing rhythm or gesture dynamics).
- Authentication: If the provided information matches the stored credentials, the user is authenticated.
- Authorization: The system then determines what resources and services the user is permitted to access based on their authenticated identity.
- Session Management: Once authenticated, the system maintains the user’s state as they navigate, often with time-based or activity-based session expirations for security.
Why Is User Authentication Important?
User authentication is critically important for several reasons, all of which contribute to the overall security and integrity of personal, corporate, and government information systems:
- Security: Authentication is the first line of defense against unauthorized access to systems and data. It helps to ensure that only authorized individuals can access sensitive information, thereby protecting against data breaches, identity theft, and other malicious activities.
- Privacy: By verifying the identity of users, authentication helps to maintain privacy by ensuring that personal information is only accessible to those with the right to view it.
- Data Integrity: Authentication helps to ensure that only authorized users can create, delete, or modify data, thereby maintaining the integrity of the data within the system.
- Compliance: Many regulatory standards require robust user authentication measures to ensure that sensitive data, such as health records or financial information, is adequately protected. Failure to comply can result in significant fines and damage to reputation.
- Non-Repudiation: Strong authentication mechanisms can provide non-repudiation, which means a user cannot deny the authenticity of their transactions or activities within a system.
- Audit and Forensics: Authentication logs are vital for auditing and forensics. They allow organizations to track who accessed what information and when was it accessed, which is crucial for investigating security incidents and for regular compliance checks.
- Reducing Fraud: Authentication reduces the likelihood of fraud by making it more difficult for unauthorized individuals to access accounts and systems to conduct fraudulent transactions.
How to Improve User Authentication?
Improving the user authentication process is a continuous process that involves adopting new technologies, refining existing protocols, and educating users.
To elevate the robustness password security of user authentication systems, consider these advanced strategies:
- Adopt Advanced Multi-Factor Authentication (MFA): Beyond traditional MFA, explore adaptive MFA that adjusts its requirements in response to user behavior and context, providing an extra layer of security while maintaining user convenience.
- Embrace Password Authentication Alternatives: Encourage the use of password alternatives like passphrases, which are easier for users to remember and harder for attackers to crack.
- Implement Continuous Authentication: Use ongoing verification methods throughout a session, not just at login, to detect anomalies that indicate potential unauthorized access.
- Leverage Artificial Intelligence: AI can detect patterns and anomalies in user behavior, providing a proactive approach to prevent breaches before they occur.
- Foster a Security-Minded Culture: Cultivate an environment where every user becomes a vigilant participant in the security ecosystem, understanding their role in protecting access to systems.
- Enhance User Education Programs: Offer engaging and regular training that includes simulations of phishing and other common attacks to prepare users to recognize and respond to threats.
Advantages and Disadvantages of User Authentification
User the authentication system is a critical component of modern information security, but like any technology, it comes with its own set of advantages and disadvantages.
Advantages of User Authentication:
- Enhanced Security: User authentication provides a fundamental security layer that helps to protect sensitive data from unauthorized access.
- Access Control: It ensures that only authorized individuals can access certain data or systems, which is crucial for maintaining data privacy and compliance with regulations.
- Audit Trails: Authentication mechanisms can track user activities, creating logs that are invaluable for auditing and monitoring purposes.
- User Accountability: By linking actions to specific user IDs, authentication helps ensure that users are accountable for their actions within the system.
- Trust in Transactions: In e-commerce and online banking, authentication builds trust between users and service providers, as it adds a level of assurance that transactions are secure.
Disadvantages of User Authentication:
- User Inconvenience: Strong authentication measures, especially those involving multiple factors, can sometimes be cumbersome, leading to user frustration or resistance.
- Cost: Implementing sophisticated authentication systems can be expensive. The hardware, software, and personnel costs can add up, especially for large organizations.
- User Education: Users need to be educated on the importance of authentication and how to use it properly, which can be challenging and time-consuming.
- Potential for Data Breach: If biometric data or other sensitive authentication information is compromised, it can be difficult or impossible to reset, unlike a password or token.
- Technical Issues: Authentication systems can sometimes fail, locking out legitimate users or, conversely, failing to block unauthorized access due to technical glitches.
User Authentication Methods
User authentication methods are diverse, each with its own unique approach to authenticate users verifying the identity of users attempting to access services and systems. A study conducted by LastPass in 2019 reported that 57% of businesses globally had implemented MFA, indicating a 12% increase from the previous year. Moreover, Adroit Market Research anticipates the market share for MFA to reach $20 billion by 2025.
Here’s a closer look at each:
Knowledge Factors
Knowledge factors involve information that only the user knows, serving as a primary authentication method because of identity verification. This category is often the first line of defense in authentication processes. It includes:
- Usernames or user IDs: Unique identifiers assigned to individuals to distinguish them from other users.
- Passwords: Secret combinations of characters known only to the user, often paired with usernames.
- Personal Identification Numbers (PINs): Numeric codes known to the user, commonly used in financial transactions.
- Answers to security questions (KBA): Personal information used to verify identity, based on previously provided answers.
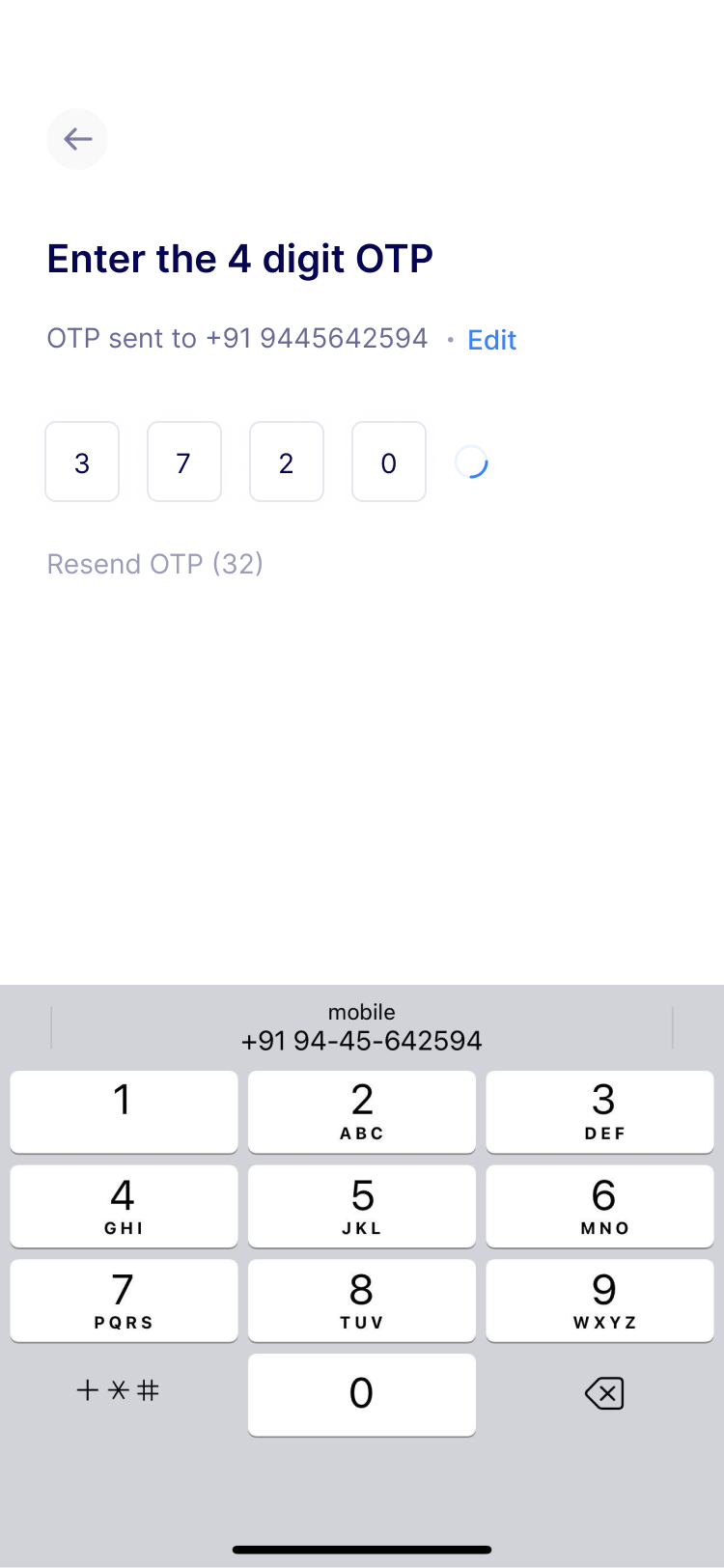
Possession Factors
Possession factors require the user to have a username and password for a specific physical item to gain access. This adds a layer of security, as it combines something the user knows with something they have. This category includes:
- Security tokens or key fobs: Physical devices that generate a one-time code.
- Smartphone apps generating OTPs: Applications that produce a unique code for each login.
- Smart cards: Cards with embedded chips that store user credentials.
- Employee ID cards: Identification cards used in organizational settings.
Inherence Factors
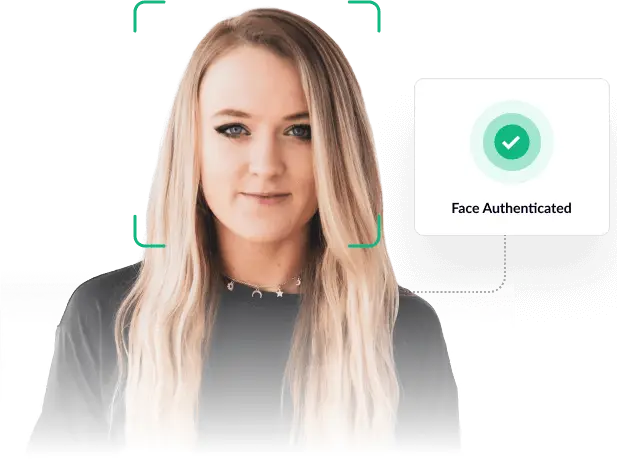
Inherence factors are biometric characteristics unique to each individual. They are increasingly popular in modern authentication systems due to their reliability and uniqueness. This category encompasses unique biological characteristics:
- Fingerprint scans: Analysis of unique fingerprint patterns.
- Retinal or iris scans: Eye scans focusing on unique features in the retina or iris.
- Facial recognition: Identification based on facial features and structure.
- Voice authentication: Verification using unique voice patterns.
Read more: What is passwordless authentication and how does it work?
Risk-Based and Adaptive Authentication
Traditional authentication treats every login attempt the same. Modern systems use adaptive authentication to dynamically adjust security requirements based on risk signals.
Risk engines evaluate factors such as:
- Device fingerprint
- IP address and geolocation anomalies
- Impossible travel scenarios
- Behavioral biometrics (typing speed, navigation patterns)
- Transaction risk scoring
If a login attempt appears low risk, the system may allow seamless access. If risk increases, additional verification such as OTP or biometric validation is triggered.
This approach strengthens security without creating unnecessary friction for legitimate users.
Location Factors
Location factors utilize the user’s geographical position as an additional security measure. This approach ensures that access online accounts is granted only when the user is in an authorized location. It typically involves:
- GPS functionality: Determining a user’s exact location via satellite signals.
- Wi-Fi and cell tower triangulation: Estimating location based on the proximity to Wi-Fi networks and cell towers.
- Geographical access restrictions: Limiting user access to certain physical locations.
Time Factors
Time factors involve the use of time-based constraints to regulate access. This method adds a temporal dimension to security, allowing access only during designated periods. It includes:
- Time-based access restrictions: Permitting user access only during certain hours or days.
- Login attempt analysis: Assessing the feasibility of a login based on the timing and location of previous sessions, such as detecting improbable travel scenarios.
User Authentication in Regulated Industries
In regulated sectors such as banking, insurance, gaming, and digital lending, authentication is directly tied to compliance and fraud prevention requirements.
For example:
- Banking platforms require multi-factor authentication for financial transactions.
- Digital lending apps must verify borrower identity before loan disbursal.
- Gaming platforms implement age and identity verification to prevent misuse.
- Crypto exchanges enforce enhanced authentication to meet AML obligations.
Strong authentication mechanisms help organizations meet regulatory mandates while protecting users from identity fraud and account takeovers.
Conclusion
In conclusion, robust user authentication is crucial for ensuring the security of online activities. By effectively combining different methods like strong passwords, security devices, biometrics, and monitoring login locations and times, we can reliably verify user identities. This is more than just a reaction to security threats; it’s a proactive approach to forging a secure and reliable digital future.
For those interested in exploring the latest in phone and biometric verification technologies, HyperVerge offers insightful resources and demonstrations. Visit our blogs to learn more about how this AI-powered ID verification tool can enhance your digital security.