Authentication confirms identity. It plays a crucial role in our online interactions as it helps protect our digital selves. Imagine it as a way of asking, “Are you really who you claim to be?”
As of this year, the Federal Trade Commission got 1.4 million reports of identity theft. This was part of a bigger picture of 5.7 million cases of fraud and identity theft. It’s clear, then, that proper authentication is vital. In our digital world, the risks of cyberattacks, identity theft, and online fraud are very real and common. Such startling figures underline a worrying trend in our digital era.
In this blog, we take a look at all of the authentication methods available today, guiding you through them in detail. From password-based systems to biometric and digital token-based solutions, we examine them in detail. We want to help you figure out which one is most appropriate for your unique needs.
Benefits of User Authentication
A user’s authentication facilitates more than just controlling access to online accounts. This article explores the authentication factors and types of sensitive information it protects, the consequences of compromised authentication, as well as the multifaceted benefits it provides:
When authentication fails, it can have severe consequences. Identity theft is a possibility, where bad actors can pretend to be someone else to deceive others. Data breaches may occur, resulting in confidential information being exposed. This can lead to significant financial losses for both individuals and companies, and may also result in legal troubles. Businesses risk damaging their reputation if they fail to protect customer data.
Read more: What is user authentication?
Benefits of Robust Authentication
Enhanced Data Security: Firstly, strong authentication guards crucial data and systems from unauthorized access. It’s like a cyber-sentry. It checks people’s identities before letting them near vital info, reducing risks of data breaches and cyber-attacks. Places like finance and healthcare, where sensitive info abounds, need this especially.
Protection of User Privacy: Strong verification plays a key role in protecting individual privacy by confirming that personal details are not accessible to unapproved people. It governs entry to sensitive facts and assists persons in keeping power over their individual information, decreasing the hazard of identity fraud and other privacy-linked troubles.
Enforcement of Compliance Standards: Lots of sectors have to follow strict data protection and privacy rules. Strong authentication can help with that (think GDPR, HIPAA, and other regulations). This way, organizations stay out of trouble with the law and avoid big fines. Compliance also demonstrates to stakeholders and customers that the organization is committed to maintaining the highest standards of data protection.
Increased Trust and Reliability: Within the digital world, establishing trust is a key resource. Companies that employ robust authentication measures demonstrate to their patrons that security and privacy are high priorities. This trustworthy approach helps form lasting bonds between organizations and consumers, as users feel assured their information is protected responsibly.
Promotion of Accountability and Traceability: Reliable verification methods confirm that each access or interaction can be connected directly to a specific user. This accountability is extremely useful, particularly in corporate settings where overseeing admittance to sensitive data is essential for security reviews, digital investigations, and upholding operational consistency.
Minimization of Financial Risks: Theft of intellectual property, sensitive business details, or consumer information from cyberattacks and data breaches can lead to considerable monetary damages. By restricting unauthorized access, strong authentication systems fulfill a critical part in protecting against such fiscal dangers. Reliable verification methods bar unlawful infiltration and safeguard prized knowledge, preventing potential financial liability from stolen accounts.
Enhancement of User Experience and Convenience: Today’s authentication methods, though protecting users, additionally give comfort. Techniques like biometrics (fingerprint, face recognition) and single sign-on (SSO) deliver a sleek and easy-to-use way to gain access to services, lessening hassle and boosting the total user experience.
Types of Authentication Methods
When it comes to keeping our online information safe, there are a bunch of different ways to do it. It’s like having different kinds of locks for your digital doors. Let’s take a look at these most common authentication methods, each one like a unique kind of lock, offering its own way to protect your stuff online.
Password-based Authentication
The most familiar form of authentication is a password. It’s like a secret handshake between you and your online accounts. It is simple yet effective and is widely used. But password authentication protocol comes with a risk because of the strength of the password itself. Weak or reused passwords can be easily cracked by fraudsters, which makes this most common authentication method vulnerable if you do not manage it properly.
Multi-factor Authentication (MFA)
Using multiple verification methods, often known as Two Factor Authentication or TFA and multi-factor authentication or MFA, substantially strengthens access security similar to passing through successive checkpoints. Gaining entry requires validation of two or more authenticating factors, such as something known (like a password), something owned (like a smartphone), and something inherent (like a fingerprint scan). This multi-layered technique meaningfully fortifies protections by necessitating hackers surmount additional barriers beyond a single sign-in credential alone.
Biometric Authentication
Biometric Authentication uses unique physical characteristics, like fingerprints or facial recognition with liveness checks, to authenticate users further. You can think of it as a key but it’s basically your body part. This method of password authentication is gaining popularity because of being highly secure and convenient and it makes it harder for intruders to mimic or steal your ‘password’.
Token-based Authentication
Token-based Authentication involves a token, a digital key, that the authentication system itself generates. It’s like getting a temporary VIP pass every time you log in. This method of mutual authentication is often used in online banking and other scenarios where high security is paramount.
Certificate-based Authentication
Certificate-based Authentication uses digital certificates to identify users. It’s same as having a digital ID card that proves who you are. This basic authentication method is commonly used in corporate environments due to its strong security and ability to authenticate devices and servers, along with users.
Passwordless Authentication
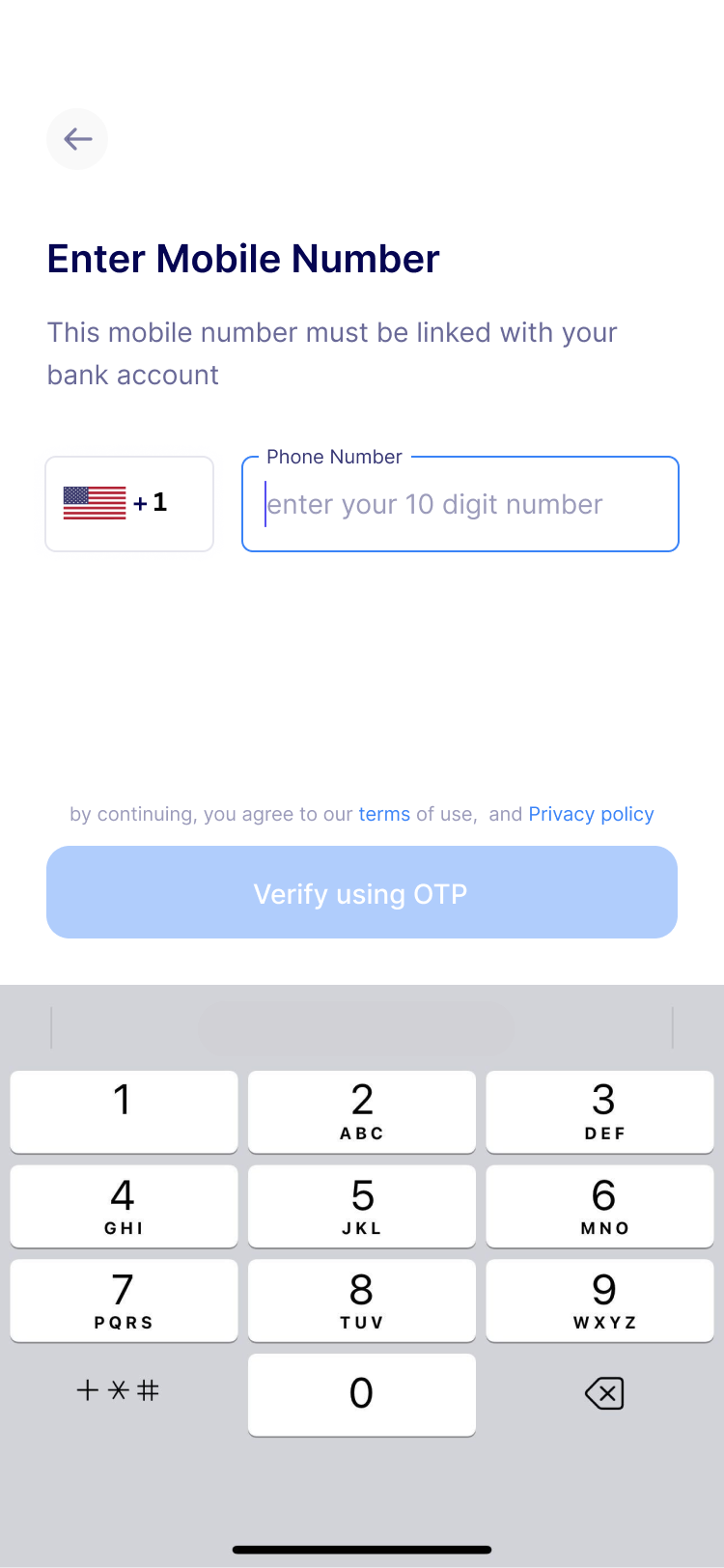
Passwordless Authentication is exactly what it sounds like – no authentication server no authentication protocol no passwords needed. Users can use a magic link sent to their email or a push notification on their phone. In simpler words, you don’t need to type passwords, offering both convenience and enhanced security.
Single Sign-On (SSO)
Single Sign-On (SSO) allows users to access multiple applications with the same password and one set of login credentials. It is like a master key for all your digital locks. It simplifies the user experience while maintaining security, which is often used in business environments to streamline access to various services.
Each of these methods plays a crucial role in protecting digital identities. From the simplicity of passwords to the sophistication of biometrics, the choice of common methods of user identification depends on the level of security needed and the context of use most secure authentication method.
How To Choose The Best Authentication Method For Your Business
Selecting the best authentication method for your business is a critical decision. It’s about striking a balance between impenetrable security and user-friendliness, all while considering the future. Let’s break down the key considerations:
Security Levels and Corresponding Methods:
- Low Security: For applications where the risk is minimal, simple password-based authentication might suffice. It’s easy to implement and user-friendly but less secure against sophisticated attacks.
- Medium Security: As the stakes rise, so should your security measures. Multi-factor Authentication (MFA), which combines something the user knows (like a password) with something they have (like a phone), offers a stronger defense.
- High Security: For handling highly sensitive data, consider advanced methods like Biometric Authentication or Certificate-based Authentication. These methods are harder to breach and are ideal for protecting critical information.
User Experience:
Balancing security with ease of use is crucial. While high-security methods like biometrics offer robust protection, they may not always be user-friendly, especially for a diverse user base. Solutions like Single Sign-On (SSO) can provide a seamless user experience without compromising on security.
Contextual Factors:
Consider your user base, the type of application, the sensitivity of the data, and device compatibility. For instance, a banking app dealing with financial transactions would benefit from biometric authentication, whereas a corporate internal tool might be better served with SSO for easier access across multiple platforms.
Cost and Implementation:
The cost and complexity of implementing an authentication method can vary greatly. While token-based common biometric authentication methods might involve additional hardware costs, methods like passwordless authentication could be more cost-effective and easier to implement.
Future-proofing:
Choose multiple authentication methods that are adaptable to evolving technologies and regulations. With the digital landscape constantly changing, your authentication method should be flexible enough to adapt to new threats and compliance requirements.
Layered Security Approach:
A layered approach to security brings together several different authentication methods to develop a more robust protection system
- Combining Methods: An effective security strategy incorporates multiple verification techniques. For example, combining biometric identifiers such as fingerprint or iris scans with facial recognition provides an additional layer of physical authentication. Document verification can authenticate that identification papers are legitimate, while detecting live characteristics helps prevent deceitful access. This multi-faceted methodology considerably diminishes chances of unauthorized entry.
- Contextual Application: In settings that require high security, like financial institutions or healthcare systems, combining biometric verification with token-based methods can provide an additional layer of protection. For internal corporate networks, SSO integrated with MFA can facilitate access while still ensuring safety.
Best Practices for Authentication Management:
MFA Policies: Regularly review and update your MFA policies. Make sure that the MFA factors used are diverse (something you know, something you have, and something you are) and that they align with the latest security standards.
Password Hygiene: Educate your team about creating strong passwords and the importance of not reusing passwords on different platforms. Implement regular password change policies and consider using password managers.
Phishing Awareness: Conduct regular training sessions to make your team aware of phishing tactics. Teach them how to recognize suspicious emails or messages and the steps to take if they encounter a potential phishing attempt.
Regular Audits: Conduct periodic security audits to assess the effectiveness of your authentication methods. This includes checking for any vulnerabilities and ensuring compliance with the latest security regulations.
Conclusion
The rise in cyber threats makes robust authentication methods crucial for safeguarding data and building trust and ensuring user privacy. It’s clear that prioritizing user security and investing in effective identity verification measures is no longer optional but a necessity for businesses.
HyperVerge’s identity verification suite offers a comprehensive solution. Sign up to see it in action!