Until 2017, Kenneth Gibson was an employee at a reputed software company. In 2018, he was found guilty of identity theft and sentenced to jail for four years.
Kenneth had the bad actor’s golden ticket – access to the private information of 8,000 people – and a diabolical plan. He set up fake PayPal accounts in the name of these people and only made small money transfers to avoid suspicions. He was eventually caught but had already netted $3.5 million by then.
This identity theft incident begs the question – could this have been avoided with a simple customer selfie during KYC? In this blog post, we explore the power of selfie identity verification which could hold the key to cutting down the $700billion+ losses from identity theft.
What is selfie identity verification?
Selfie identity verification is a biometric verification process that confirms a person’s identity.
Here’s how selfie verification works: a person takes a selfie and uploads it to the selfie verification tool. The photo is matched against a photo ID like a passport or a driver’s license using AI-powered software. The software analyzes each photo and converts them into digital data. It compares the data to match distinct facial characteristics and decides if it’s the same person.
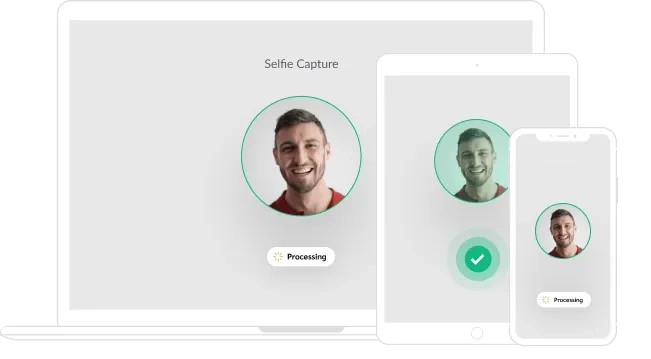
Selfie ID verification is simple and doesn’t exert a lot of cognitive load on the user. They only have to take a picture of themselves and their government-issued ID, the software does the rest. It’s user-friendly and secure, a win-win for both companies and users.
The best form of selfie identity verification entails liveness detection. It kills the loophole of selfie verification methods – spoofing attacks. Bad actors use masks, photo cut-outs, and other presentation methods to assume others’ identities. Liveness detection asks the person to perform a certain set of actions or monitor the skin texture passively to verify if the person is real.
When to selfie identity verification?
Here are the three areas where selfie checks are an amazing tool to verify someone’s identity:
Customer onboarding
Selfie verification serves as the perfect medium to smoothen the onboarding process and make it more secure. This is more applicable to financial institutions and e-commerce companies expanding digital businesses to present a consistent experience to their customers
Age verification
The age verification process is essential for online gaming and dating websites. A real-time selfie of a person compared with the government ID details keeps the company safe from giving access to minors. Because the process is effortless, it doesn’t flip out users who meet the age criteria.
Account recovery
Anyone getting kicked out of their account would be desperate to regain access. However, any form of vulnerability during account recovery could result in spoofing attacks. A selfie to prove the actual identity of the person builds an extra layer of safety to prevent such attacks. All they have to do is upload their real time selfie while recovering their account.
Benefits of selfie identity verification
There are five areas where selfie identity verification provides the maximum benefit:
Protection against database breaches
Selfie identity verification has a direct approach to security. It keeps your database safe using biometric technology to confirm a person’s identity. The avoidance of database breaches maintains the sanctity of the data and helps you earn your customer’s trust.
Low-friction verification
The selfie verification process doesn’t go back and forth. There are no multiple ID checks or complex password database verification. The biggest advantage is neither the user experience is compromised nor your security standards.
It’s a perfect example of how advanced real-time face detection technology streamlines and secures your user verification process in multiple digital platforms.
Improved user experience
The biggest problem with traditional methods of identity verification is that they demand users to go through complex processes like submitting multiple documents or being physically present at a location.
Selfie verification doesn’t demand any of that. The user only has to click a photo which they can do from the comfort of their home. This doesn’t interfere with the user’s experience, on the contrary, they have a positive feeling on the overall fluidity of the verification process.
Remote identity verification
The finance, healthcare, and e-commerce industries have huge benefits of using selfies to verify identity remotely. As each industry expands its footprints into the digital space, selfie verification could end in-person identity checks.
This is a positive sign for scaling their business into geographical areas they couldn’t reach earlier while maintaining high-security standards.
Reduced fraud
Selfie verification makes it challenging for fraudsters to steal someone else’s identity and confirms that the person is present during the verification process. It doesn’t put pressure on the organization’s workforce because the process takes place automatically in AI face recognition software.
How does selfie verification work: step-by-step process
Completing a selfie ID verification process is a straightforward process designed for security and simplicity. It is a user-friendly experience for onboarding new customers or securing financial transactions. Below is a comprehensive guide to the typical selfie identity verification process.
- Capturing Government-Issued ID: You need a clear photo of the user’s government-issued identification, such as a driver’s license or passport. This step often involves using a smartphone or tablet to capture a high-quality image in good lighting.
- Uploading the ID: The next step is to upload the photo of the ID to a selfie identity verification solution. This could be a mobile app or a web portal. Ensure the image is clear and all relevant information is visible.
- Taking a Live Selfie: Following the upload, the user will be prompted to take a live selfie. This usually involves facing their device’s camera and following on-screen instructions. The aim is to capture your live physical presence, which is crucial for the next step.
- Performing Liveness Detection: The system will then perform a liveness check to ensure that the selfie is indeed live and not a photograph or video. This is where sophisticated algorithms come into play, analyzing the selfie for signs of real-time human presence.
- Face Matching: The software compares the live selfie with the photo on your uploaded ID. It uses facial recognition technology to verify that the person in the selfie and the ID document are the same.
- Validation and Approval: If the comparison is successful and no discrepancies are found, the system will validate the verification process.
- Continuous Authentication: For returning users, some platforms may use the initial verification to reauthenticate users quickly, creating a smooth and secure ongoing experience.
Is selfie identity verification foolproof?
Using selfies as an identity verification solution is a great idea but it has limitations. Here are the two most popular pitfalls that you should be aware of:
Possibility of spoofing
Spoofing attacks occur when fraudsters try to trick the identity verification system by using manipulated images. There are different ways fraudsters do that. For example, in the Image-of-Image fraud technique, scammers take a picture of an ID document displayed on a screen or printed on paper and present it as their own. This is the most popular form of document fraud technique, occurring in 63% of the IDs that were rejected.
Requires additional verification layers for high-risk scenarios
If you look at selfie verification in isolation, it’s a potent technique to save your business from identity theft attacks. However, in high-risk scenarios like high-value financial transactions or situations where bad actors could get access to sensitive information, selfie verification might not be enough.
This is especially true for industries that function within the tightropes of regulatory compliance. In such a case, supporting selfie verification with other verification methods like video verification and behavioral biometrics will help you build a solid security system against identity fraud.
Best practices for selfie identity verification
How can you make the selfie verification process better? Here’s what our experts have to say about it:
Perform liveness detection checks
Both active and passive liveness checks will determine if the individual is present in real-time and not a spoof. Here are a few active detection techniques that fraud prevention software usually use:
- Speak out the text displayed on the screen
- Hold a piece of paper where they write down some verification text
- Perform gestures such as moving their head up and down, left and right, blinking, etc.
Passive liveness, on the other hand, silently analyzes the video feed for signs of life, such as subtle facial movements or texture analysis.
- Speak out the text displayed on the screen
- Hold a piece of paper where they write down some verification text
- Perform gestures such as moving their head up and down, left and right, blinking, etc.
Passive liveness, on the other hand, silently analyzes the video feed for signs of life, such as subtle facial movements or texture analysis.
- Speak out the text displayed on the screen
- Hold a piece of paper where they write down some verification text
- Perform gestures such as moving their head up and down, left and right, blinking, etc.
Passive liveness, on the other hand, silently analyzes the video feed for signs of life, such as subtle facial movements or texture analysis.
Use robust AI models to avoid bias
The more accurate your AI models are, the more precise the results will be. This is an uncompromised requirement if a large volume of identification processes are run daily. Train your AI models on diverse datasets, and focus on including a mix of individuals from different genders, races, and ethnicities.
Use selfie identity verification as an additional verification layer
Look at selfie verification as an extra pair of hands to protect your business from identity thefts. Use it in your multi-factor authentication process, but make sure it syncs with your existing methods of document verification and database checks.
How to add selfie identity verification to your KYC workflow?
Integrating selfie identity verification into your Know Your Customer (KYC) workflow significantly enhances the security and integrity of sensitive data in your customer verification process.
Deploy a robust identity verification tool that has a powerful face recognition engine. For instance, HyperVerge’s face authentication has been rated in the top 10 globally by NIST.
To build a comprehensive and robust KYC workflow, include a variety of verification methods:
- Document Verification: Start by verifying the authenticity of government-issued IDs or documents. This step confirms that the document is valid and has not been altered or forged.
- Email Verification: Ensure the user’s email address is active and accessible. This also helps in re-verifying the identity if needed.
- Phone Verification: Similar to email, verify the phone number to ensure it is in service and owned by the user. This also adds a layer of security and a direct line of communication with the customer.
- Captcha Detection: Incorporate Captcha to prevent automated bots from creating accounts or accessing services, ensuring that a real person is attempting the verification.
- Trusted Identity Network: Leverage a network of verified identities, often powered by blockchain technology, to validate that the user’s provided information is trustworthy and has been verified by other reliable sources.
- Multi-Factor Authentication (MFA): Combine something the user knows (like a password), something the user has (like a phone), and something the user is (like a biometric feature) to create a layered defence against unauthorized access.
- Other Biometric Methods: Beyond selfies, leverage other biometric verification methods such as fingerprints, voice recognition, or iris scans to confirm identity. These methods provide unique physiological data that are extremely difficult to replicate or forge.
For more information, explore our detailed guide to identity verification and how HyperVerge can help.
Takeaways
Selfie verification is a strong verification method to safeguard your business from spoofing attacks and bad actors. It’s quick to implement, effortless for your users, and keeps your system safe from data breaches. However, selfie verification systems give the best results when they fit perfectly into your existing KYC process.
But, it’s easier said than done. You need an advanced, AI-powered identity verification solution like HyperVerge that takes end-to-end care of your KYC process. It merges selfie verification with passive and active liveness checks and takes care of email and phone verification automatically. It’s the perfect ally for businesses looking for robust tools to scale their identity verification process without hampering the user experience.
Curious how HyperVerge will fit into your KYC process? Book a demo now.