First-party fraud occurs when an individual commits fraud by misrepresenting themselves or their intentions while using their own details. Here, unlike other types of fraud, the person committing the fraud and the person whose account is used are the same.
First-party fraud can have severe impacts on businesses. They can result in heavy chargeback fees, which accumulate and are non-refundable, regardless of whether the claim is valid. When defrauded items are not returned, or if they are unsellable when returned, businesses can face inventory losses.
Furthermore, the operational costs of processing and shipping products and transactional expenses add to credit risk and overhead losses. Banks and processors may raise concerns when a business’s chargebacks become too high, resulting in increased scrutiny and sometimes frozen accounts. These risks can cause financial losses and adversely impact a business’s reputation.
Definition of first-party fraud
First-party fraud occurs when the customers themselves commit the fraud, not an external scammer or criminal organization. This type of fraud can be unintentional due to a misunderstanding. Or it can be a deliberate act. Regardless of the intent, it is the business that ultimately bears the losses.
There are various types of first-party fraud, such as chargeback, friendly, and application fraud. A classic example of first-party fraud is providing false personal details to get loans.
Another type of credit card fraud is bust-out schemes. This happens when a fraudster opens an account with genuine information, establishes a good credit history, and then maxes out the credit limits without intending to repay the debt.
Sometimes, buyers may initiate a chargeback due to confusion- this falls under unintentional first-party fraud. They do not realize their actions still qualify as fraud.
At other times, customers may indulge in opportunistic first-party fraud. They exploit situations for personal gain, like claiming unauthorized purchases made by family members. They might not intend to harm, but they cause damage nonetheless.
Identifying and preventing any form of first party third-party fraud is crucial because it leads to heavy financial losses plus loss of inventory. Moreover, you run higher risks of scrutiny and regulation challenges. It is, therefore, important for businesses to implement fraud detection and prevention strategies that work to safeguard against these risks.
Examples of first-party fraud
Chargeback fraud
Chargeback fraud is also known as friendly fraud. It occurs when a customer buys something with a credit or debit card and asks the bank to refund their money even after getting the product. They keep both the product and the money.
Ghost funding
Ghost funding involves creating fake transactions or accounts to trick individuals into believing funds exist.
For online merchants, ghost funding can occur when customers fund purchase accounts using ACH (Automated Clearing House) transfers, accessing these funds for purchases before the money has settled officially. They exploit this by making purchases from accounts that lack sufficient funds.
De-shopping
De-shopping is when someone buys items to use once and then returns them for a full refund. In the specific case of clothes, when someone deliberately purchases clothes to use them once or twice and then returns them for a full refund, it is called wardrobing.
Fronting
Fronting is common in insurance. When someone registers something, like car insurance, under another person’s name, which seems less risky, to save money. For example, a parent might use their name for their child’s car insurance to get lower premiums. This messes up the insurance company’s risk calculations and can lead to massive losses if a claim does rise.
Lost in transit fraud
Goods lost in transit fraud is when a customer claims that the products they ordered online were never delivered or arrived damaged. Some may even send back empty boxes to claim refunds. It causes businesses to lose money if they keep up good customer service or risk upsetting customers by making delivery and return policies stricter.
How does first-party fraud work?
The basic premise of how first-party fraud works is that an individual (sometimes it can be an organization) falsifies or misrepresents their information for financial gain.
A fraudster may use fake information to obtain goods, funds, or a service, promising to pay for them later but failing to do so. Alternatively, they devise ways to get their money back after they have paid.
It can play out in two ways:
Unintentional first-party fraud
Sometimes, legitimate customers commit fraud without meaning to. They may confuse a chargeback, a formal dispute of a charge on their account, with asking for a refund. The customer might be upset or confused about what they bought. Or they may not understand the store’s rules for returning items.
In these cases, there is no intent to deceive; the customer just does not realize the impact of their mistake.
Intentional first-party fraud
In some cases, honest customers might commit fraud when they see an easy opportunity to benefit without proper justification.
- The customer might not be happy with their purchase
- Someone like a family member could have used their account without their knowledge
- They might find the refund process too difficult or time-consuming
- They might want to keep an item without paying for it
While some customers only seize the opportunity when they stumble upon one, others plan to commit fraud, fully aware of their deception from the start. Tactics like cyber shoplifting or wardrobing, where customers use and return items pretending they are unused, are common. The fraudsters use their real identities but with the plan to manipulate the system for unwarranted gains.
These are deliberate and calculated attempts to defraud, causing significant losses to businesses. Businesses can develop targeted strategies to detect and prevent first-party fraud risk by first understanding the first-party fraud schemes. Ultimately, it helps in protecting resources and honest customers.
What is the difference between first, second, and third-party fraud?
To differentiate between first, second, and third-party fraud, let’s look at who commits the fraud and the nature of the action.
First-party fraud
The first party fraud detection is committed by the individual directly involved as the customer. So, the first-party fraudsters are the customers themselves.
They misrepresent their intentions or financial status to obtain services or money with no intention of fulfilling their part of the agreement. Examples are bust-out fraud, chargeback fraud, and fronting.
Second-party fraud
In second-party fraud, the criminal is the person close to the victim- usually a friend or family member. In some cases, it is a person whom the victim knowingly gives details.
They use the victim’s data for personal gains. Occasionally, the vulnerable victim allows the fraudster to use their details- by naively trusting them or in exchange for a small fee. In other cases, the scammer takes the details of their known person and commits second-party fraud. Examples include family member identity theft, money laundering, and scammer transfers.
Third-party fraud
Third-party fraud is committed by an external entity or person who is not the customer or directly connected with the other party.
Third-party fraud is often sophisticated and includes activities like identity theft, where fraudsters steal someone’s personal information to carry out unauthorized transactions, or large-scale data breaches affecting multiple people. Examples include ATO (account takeover fraud), loan stacking, and synthetic identity theft.
How to protect against first-party fraud?
Implement the following strategies to prevent first-party fraud:
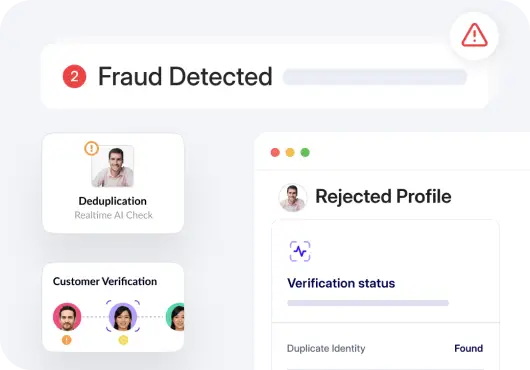
Choose the best AI fraud detection software
Invest in AI fraud detection software that leverages machine learning to identify unusual patterns and behaviors in real-time. Look for solutions that offer continuous learning capabilities to adapt to new fraudulent tactics. Opt for one that can integrate with your existing systems for seamless data analysis.
Implement the best OCR and document verification solution
Deploy optical character recognition (OCR) and document verification technologies to prevent fraud. Intelligent identity verification helps fight digital fraud at several levels. These tools should verify document authenticity and accurately extract data. Your chosen solution should:
- Support different types and formats of document.
- Have a high accuracy when it comes to data extraction and verification.
- Ensure secure and compliant handling of data.
Regularly monitor the transactions
Regular monitoring of transactions is essential for effective fraud detection and prevention. Set up a system that instantly alerts you about suspicious activities. It should observe transaction patterns to identify anomalies.
Fight against first-party fraud with automated solutions
When choosing fraud detection software, companies must focus on specific features that address the unique challenges posed by this type of fraud.
Firstly, behavioral analysis capabilities are crucial. First-party fraud has seemingly many legitimate payment transactions made with genuine information. Therefore, software that can analyze behavioral patterns in customer identity verification over time to detect anomalies indicative of fraud is essential. Look for solutions that leverage advanced analytics to understand normal user behavior and identify deviations that may signal fraud.
Next, the software should integrate seamlessly with existing data systems to leverage all available customer data for accurate fraud detection. This integration allows for a comprehensive view of customer activities across multiple active users and different channels, which is essential for detecting subtle signs of first-party fraud.
Finally, real-time processing is also vital. Immediate detection of fraudulent activities helps prevent losses before they escalate.
Since first-party fraud tactics evolve rapidly, the detection software must use machine learning algorithms that adapt to new fraud patterns and tactics as they emerge. This adaptability helps in maintaining a high detection accuracy over time.
HyperVerge utilizes advanced AI/ML technology that frequently updates to identify new fraud tactics, which helps effectively combat complex first-party fraud. Our solutions operate in real-time, which is critical for immediately stopping fraudulent activity and reducing potential damage.
To strengthen your defense against first-party fraud, try HyperVerge’s identity verification solutions. Sign up today to take the first step toward reliable fraud management.